MicroZAccess Architecture and Components
COSGrid ZTNA operates on the principle:
Never Trust. Always Verify. Continuously Validate.
Access flow logic:
The user initiates the connection.
Identity is verified.
Device posture is validated.
Policy engine evaluates contextual rules.
Application-specific access is granted or denied.
Continuous session monitoring is maintained.
All enforcement decisions are real-time and policy-driven.
Component Architecture
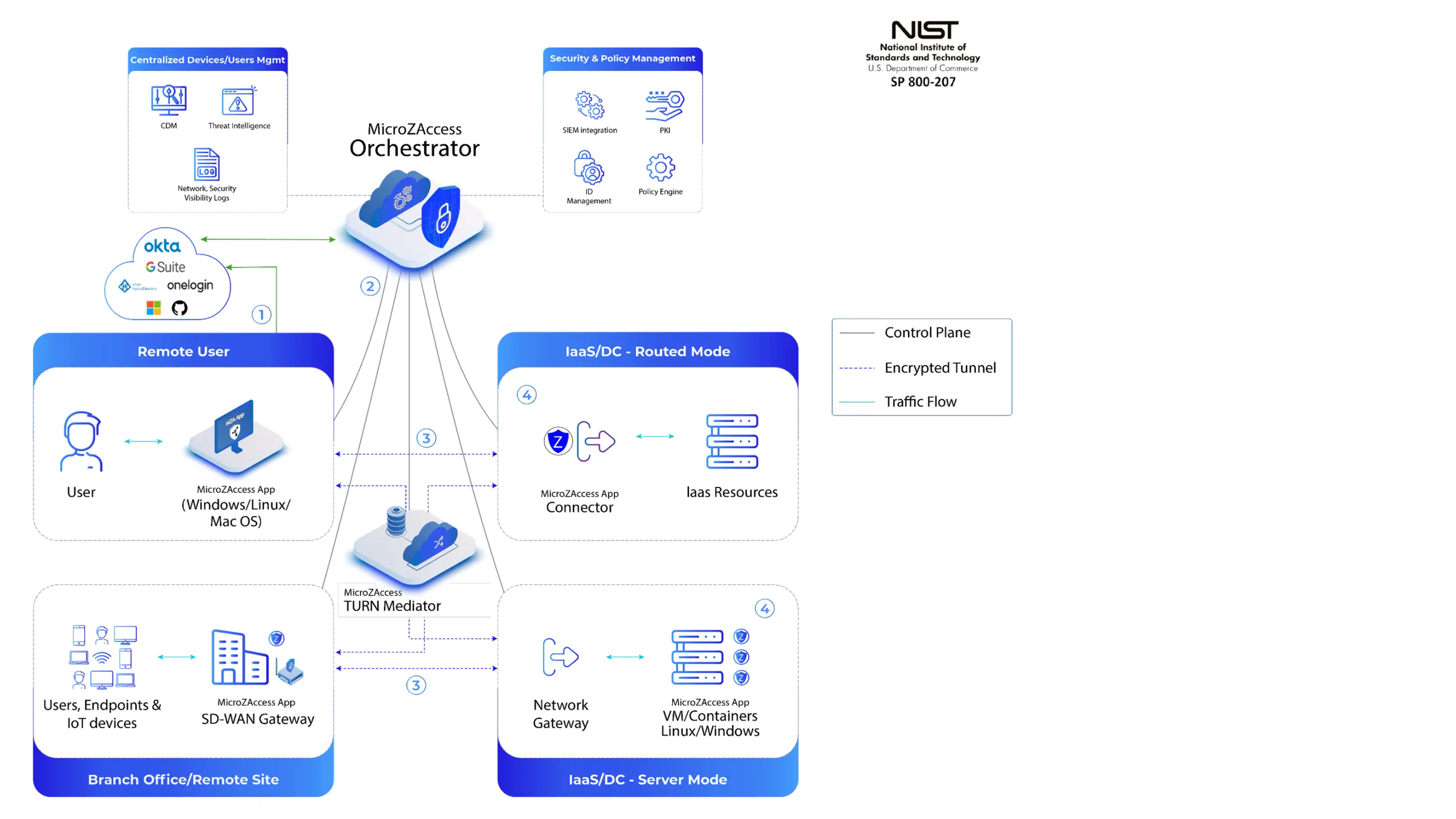
1. ZTNA Client (Endpoint Agent)
Installed on user endpoints.
Performs device posture checks.
Communicates with the policy controller.
Enforces local policies.
2. COSGrid Policy Controller
Central decision engine.
Evaluates identity + context + device posture.
Pushes enforcement rules dynamically.
3. Secure Application Gateway
Protects internal applications.
Enables application-layer access without exposing network.
4. Identity Integration Layer
Integrates with enterprise directory systems.
Supports SSO, MFA, and federation.
5. Logging & Analytics Engine
Real-time session visibility.
User activity tracking.
Compliance audit logs.
Workflow Integration
ZTNA integrates seamlessly into existing enterprise ecosystems:
Active Directory / LDAP
Cloud IdP (Azure AD, Okta, etc.)
SIEM platforms
Endpoint security tools
Firewall and SASE architecture
Integration ensures:
No infrastructure overhaul required.
Gradual migration from VPN.
Policy alignment across network layers.